Imagine buying a coffee with a digital coin, then somehow using that exact same coin to buy lunch later. In the physical world, this is impossible because you hand over the cash. But in the digital realm, data is just code-it can be copied and pasted instantly. This is the double-spending problem, and it was the biggest hurdle standing between Bitcoin and becoming a real currency.
Before blockchain, we relied on banks and credit card companies to act as gatekeepers. They kept a central ledger that said, "Alice has $10, she spent $5, so now she has $5." If Alice tried to spend that $5 again, the bank’s computer would reject it. But if you want a decentralized system-one without a middleman-who decides if a transaction is valid? That’s where consensus mechanisms come in. They are the rules that allow strangers on a network to agree on the truth without needing to trust each other.
The Core Problem: Why Digital Money Needs Rules
To understand how consensus works, you first have to understand why double-spending is such a nasty bug. Digital files are non-rivalrous. You can email a PDF to ten people, and all ten get a perfect copy. Money doesn’t work that way. If I send you one dollar, I should no longer have that dollar.
In early digital cash experiments in the 1980s and 90s, this was unsolved. Attackers could create two transactions spending the same token and broadcast them simultaneously. If the network processed both, the attacker effectively created money out of thin air. This would destroy confidence in the currency instantly.
Satoshi Nakamoto solved this in 2008 not with a new type of encryption, but with a new type of agreement. The solution wasn't just about cryptography; it was about economics and timing. By linking transactions together in a chain and making it expensive to alter that chain, Nakamoto created a system where honesty became the most profitable path for participants.
Proof of Work: Security Through Energy
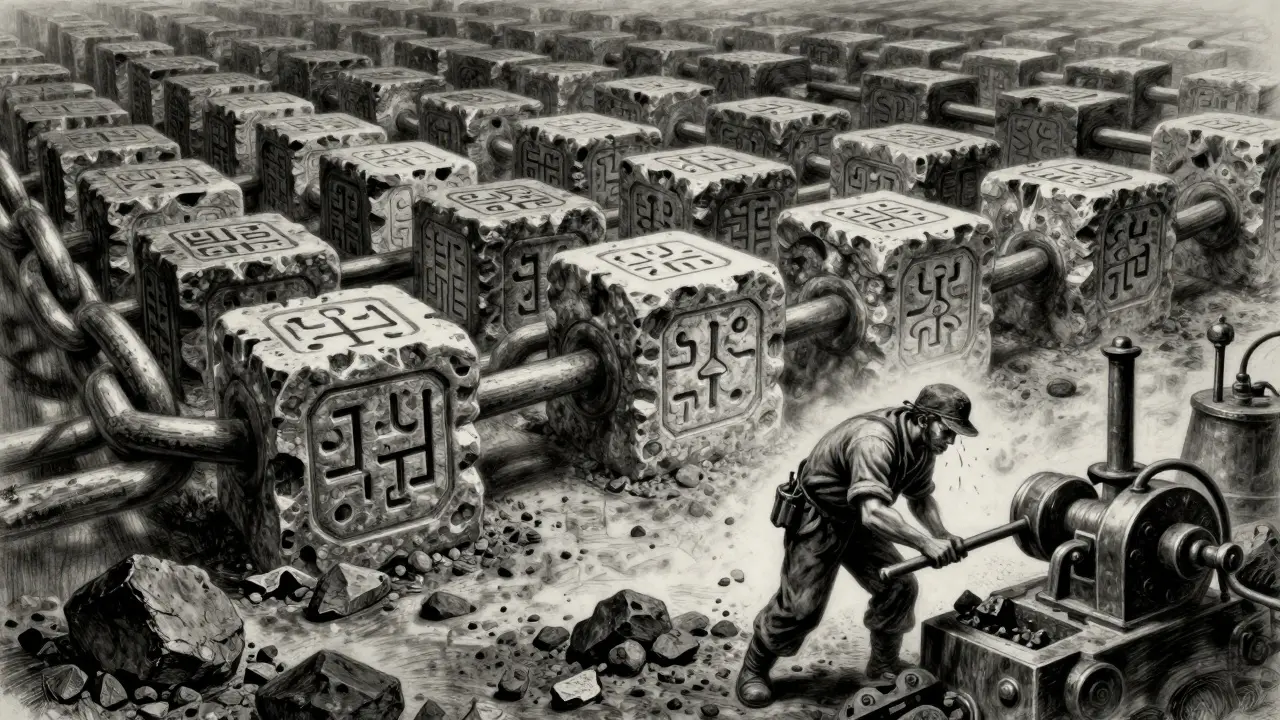
The original mechanism used by Bitcoin is called Proof of Work (PoW). It’s a brute-force approach. Imagine a global lottery where every miner is buying tickets. To buy a ticket, you have to solve a complex mathematical puzzle. The first person to solve it gets to add the next block of transactions to the blockchain and earns a reward.
How does this prevent double-spending? It makes changing history incredibly expensive. Let’s say an attacker tries to double-spend a Bitcoin they sent to a merchant. They would need to:
- Create a secret chain of blocks that excludes the payment to the merchant.
- Catch up to the public chain’s length.
- Broadcast their fake chain before the honest network adds more blocks.
To do this, the attacker needs more computing power than everyone else combined-known as a 51% attack. On a large network like Bitcoin, this requires billions of dollars in specialized hardware and massive electricity bills. It’s economically irrational. The cost of the attack far exceeds the value of the coins being double-spent.
The downside? PoW is energy-intensive. Critics point out that this level of security comes at a high environmental cost, which has driven the industry toward more efficient alternatives.
Proof of Stake: Security Through Collateral
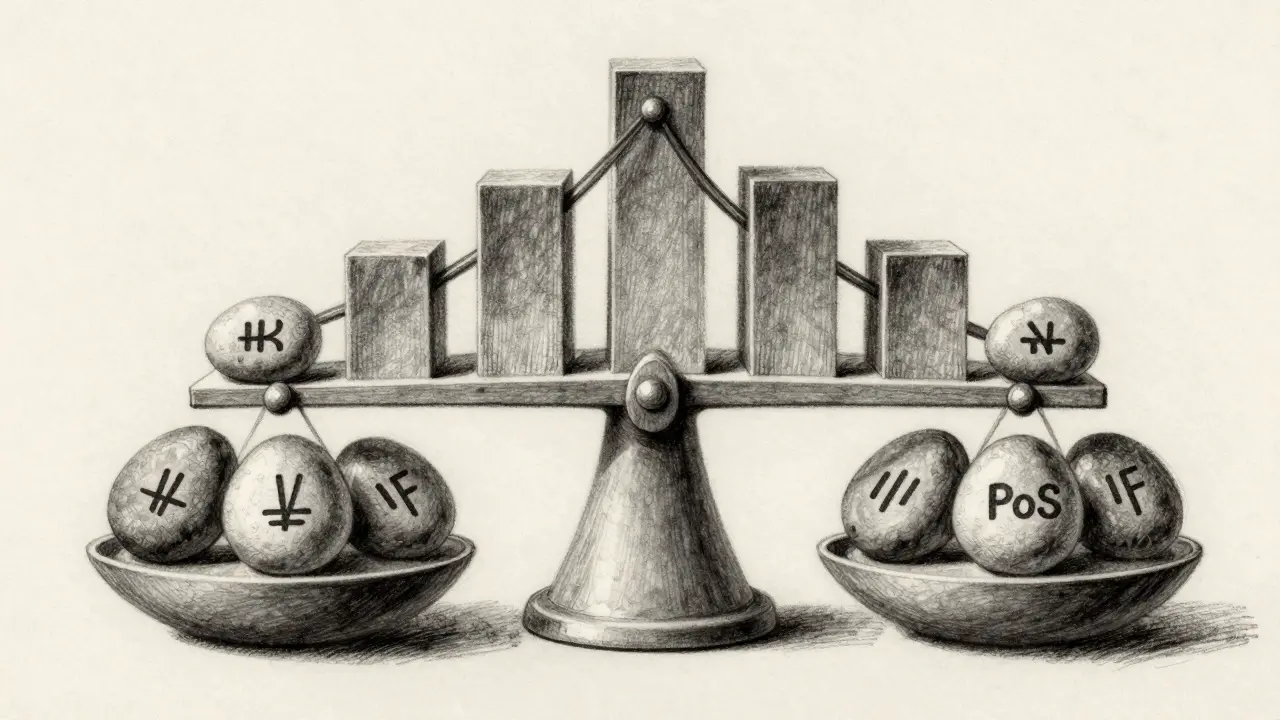
Enter Proof of Stake (PoS), the mechanism Ethereum adopted in 2022 during its "Merge." Instead of miners burning electricity to solve puzzles, validators lock up (or "stake") their own cryptocurrency as collateral. The protocol randomly selects validators to propose blocks based on how much they’ve staked.
PoS prevents double-spending through economic disincentive rather than computational difficulty. If a validator tries to cheat-for example, by trying to validate two conflicting blocks-they risk having their entire stake slashed (confiscated). This is often called "slashing conditions."
Here’s the logic: If you control 10% of the network’s stake, you also hold 10% of the network’s total value. If you try to double-spend and destroy the network’s credibility, the value of your stake crashes. You lose everything you were trying to gain. It aligns the interests of the validators with the health of the network.
| Feature | Proof of Work (PoW) | Proof of Stake (PoS) |
|---|---|---|
| Security Source | Computational Power & Energy Cost | Economic Collateral (Stake) |
| Double-Spend Barrier | Requires majority of hash rate (expensive hardware) | Requires majority of tokens (economic loss via slashing) |
| Energy Usage | High | Low (~99.9% less than PoW) |
| Finality Speed | Probabilistic (requires multiple confirmations) | Faster finality possible with modern protocols |
The Role of Transaction Finality
Consensus isn’t instantaneous. When you send a crypto transaction, it’s not "done" the second you click send. It enters a mempool-a waiting room for unconfirmed transactions. A validator picks it up and includes it in a block. But even then, it’s not fully safe yet.
This is where Transaction Finality comes in. In PoW systems like Bitcoin, finality is probabilistic. Each new block added on top of your transaction makes it harder to reverse. After six blocks (about an hour), the probability of a reorganization (a double-spend attempt) becomes statistically negligible. Merchants often wait for these confirmations before shipping goods.
In PoS systems, finality can be faster and more deterministic. Some networks use checkpointing or Casper-like finality gadgets that mathematically guarantee a block cannot be reverted unless a huge portion of the network actively colludes to break the rules. This reduces the window of opportunity for double-spending attacks significantly.
Hybrid Models and Future-Proofing
Not all networks choose sides. Some use hybrid models to combine strengths. For instance, Decred uses PoW for block production to ensure decentralization of mining, but PoS for voting on governance and treasury funds. This creates a check-and-balance system where neither group can dominate completely.
Another emerging trend is Delegated Proof of Stake (DPoS), used by networks like EOS. Here, token holders vote for delegates who validate transactions. It’s faster and more scalable, but it introduces a different risk: centralization. If only a few large entities hold the votes, the barrier to double-spending might be lower if those entities decide to collude.
As quantum computing advances, researchers are already looking at quantum-resistant signatures. While consensus mechanisms handle the agreement layer, the underlying cryptographic signatures must also remain secure to prevent identity theft, which could facilitate sophisticated double-spending vectors.
Real-World Risks and Mitigations
No system is perfect. Smaller blockchain networks with low market caps are vulnerable to 51% attacks. There have been instances where attackers rented hash power to reverse transactions on smaller PoW chains. Similarly, on some PoS chains, if the total value staked is low, an attacker might buy enough tokens to control the network, double-spend, and then dump the tokens.
To mitigate this, users and businesses should:
- Wait for Confirmations: Never treat a zero-confirmation transaction as settled for high-value items.
- Monitor Network Health: Check the hashrate (for PoW) or active stake (for PoS) of the network you’re using.
- Use Layer 2 Solutions: Platforms like Lightning Network (for Bitcoin) or rollups (for Ethereum) add additional security layers and speed up settlements, reducing exposure time.
Can double-spending happen on Bitcoin?
Theoretically, yes, but practically, it is nearly impossible for large amounts. An attacker would need to control more than 51% of the network's computing power, which costs billions of dollars. For small, instant transactions, there is a tiny risk if you don't wait for confirmations, but for standard usage, Bitcoin is considered secure against double-spending.
What is the difference between PoW and PoS regarding double-spending?
In Proof of Work, preventing double-spending relies on the high cost of electricity and hardware. In Proof of Stake, it relies on the financial penalty of losing your staked coins (slashing). PoS is generally more energy-efficient and offers faster finality, while PoW has a longer track record of security.
Why do merchants wait for 6 confirmations?
Each confirmation adds another block on top of the transaction containing your payment. Reversing a transaction requires redoing the work for that block and all subsequent blocks. After 6 blocks, the computational effort required to reverse the transaction is so high that it is economically unviable for any attacker.
Is Proof of Stake safer than Proof of Work?
Both are highly secure when implemented correctly on large networks. PoS reduces the risk of long-range attacks and is more sustainable. However, PoW has been battle-tested for over a decade. The safety depends more on the size and decentralization of the network than the specific mechanism itself.
What happens if a validator tries to double-spend in a PoS network?
They face "slashing." Their staked tokens are automatically detected by the protocol as malicious behavior and are burned or redistributed to honest validators. This acts as a strong financial deterrent against cheating.