ECDSA vs RSA Key Size Calculator
Discover the key size equivalence between ECDSA and RSA. A 256-bit ECDSA key provides the same security as a 3072-bit RSA key. See how much smaller ECDSA keys are while providing equivalent security strength.
Equivalent Key Sizes
Based on the article's statement: A 256-bit ECDSA key provides the same security as a 3072-bit RSA key (12:1 ratio).
What Is ECDSA and Why Does It Matter in Bitcoin and Ethereum?
ECDSA stands for Elliptic Curve Digital Signature Algorithm. It’s the math that lets you prove you own your Bitcoin or Ethereum without ever revealing your private key. Think of it like a digital fingerprint only you can make - and everyone else can verify. Without ECDSA, blockchain wouldn’t work. There’d be no way to know if a transaction really came from you, or if someone else was pretending to be you.
Both Bitcoin and Ethereum use ECDSA to sign every transaction. When you send 0.5 ETH or 0.1 BTC, your wallet uses your private key to create a unique signature. Miners and validators check that signature against your public key to confirm you’re authorized. It’s fast, secure, and uses tiny amounts of data compared to older systems like RSA.
The reason ECDSA was chosen? Efficiency. A 256-bit ECDSA key gives the same security as a 3,072-bit RSA key. That means less storage, faster verification, and lower fees - critical when you’re processing millions of transactions daily.
The Same Curve, Different Hashes: Bitcoin vs. Ethereum
Bitcoin and Ethereum both use the same elliptic curve: secp256k1. This curve is defined by the equation y² = x³ + 7 over a giant prime number. It’s not random - it was carefully selected for speed and security. The base point G, the curve order n, and all the math underneath are identical in both blockchains.
But here’s where they split: hash functions.
Bitcoin takes your transaction data and runs it through SHA-256 - twice. That’s called double hashing. It’s simple, proven, and has been running since 2009 without a single cryptographic break. SHA-256 is the same algorithm used in Bitcoin mining, so it’s deeply baked into the system.
Ethereum, on the other hand, uses Keccak-256. This isn’t SHA-3 exactly - it’s a variant that was submitted to NIST’s SHA-3 competition and later slightly modified. Ethereum chose it because it’s faster on standard CPUs. Benchmarks show Keccak-256 processes data about 15% faster than SHA-256 on modern Intel chips. That speed adds up when you’re handling smart contracts, token transfers, and complex transaction types.
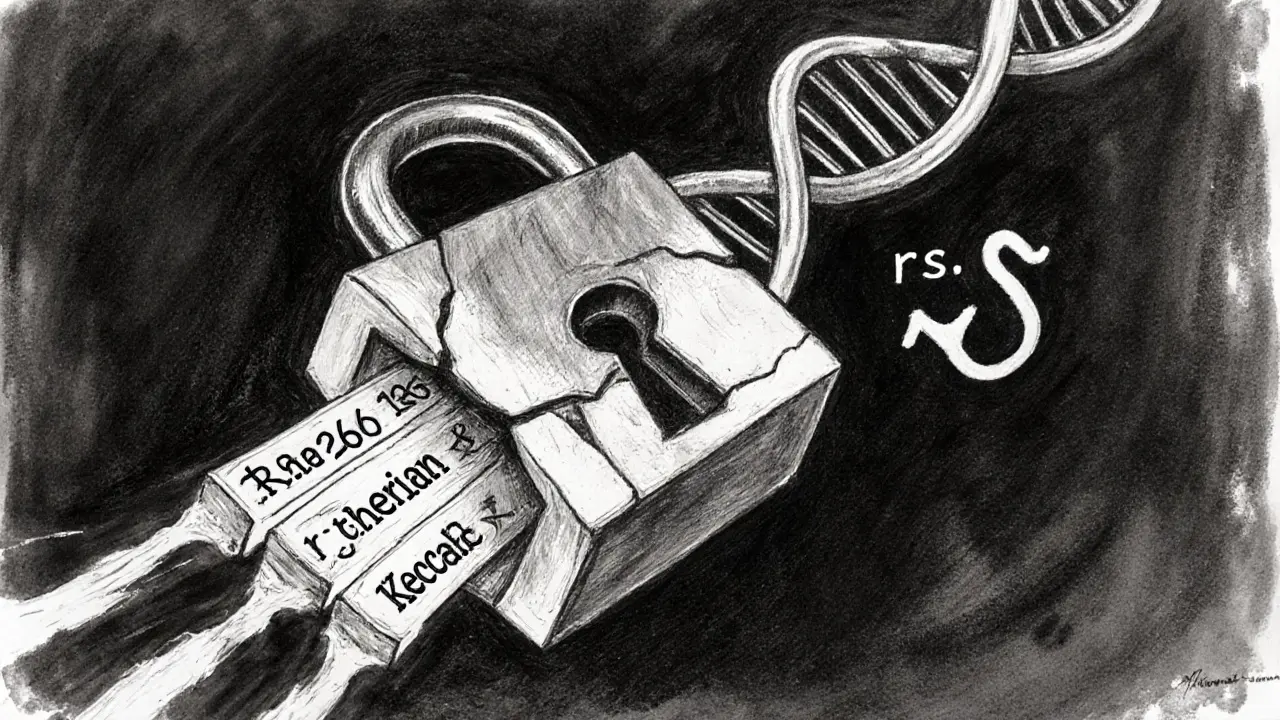
So even though the signing math is the same, the input to that math is different. That’s why a Bitcoin signature won’t work on Ethereum, and vice versa. They’re using the same lock, but different keys.
How ECDSA Signatures Are Made - Step by Step
Here’s what actually happens when you hit “Send” in your wallet:
- Your wallet takes the transaction data - who’s sending, who’s receiving, how much, gas fees, etc.
- It hashes that data: Bitcoin uses double SHA-256; Ethereum uses Keccak-256.
- It generates a random number, called k. This is critical. If this number is reused or predictable, your private key is exposed.
- Using ECDSA math, it combines your private key and k to generate two numbers: r and s.
- These two numbers form your signature - a 64-byte chunk attached to your transaction.
- Anyone on the network can verify it using your public key and the original transaction hash.
That’s it. No passwords. No servers. Just math.
But here’s the catch: k must be truly random. If two signatures ever use the same k with the same private key, an attacker can calculate your private key in seconds. This isn’t theoretical - it happened in 2011 with early Bitcoin wallets. Over 2,000 BTC were stolen because of poor random number generation.
Why Randomness Is the Weakest Link
ECDSA is mathematically sound. The problem isn’t the algorithm - it’s the implementation.
In 2010, Sony’s PlayStation 3 was hacked because their ECDSA implementation reused the same k for every signature. Attackers recovered the private key and started pirating games. The same flaw caused Bitcoin thefts in 2011 and 2012. Android’s SecureRandom bug in 2012 led to over 500 wallets being drained.
Today, most wallets use RFC 6979 - a method that generates k deterministically from your private key and the message being signed. No randomness needed. No chance of reuse. This fix is now standard in Ledger, Trezor, and modern software wallets.
But legacy wallets still exist. If you’re using an old mobile wallet from 2015, you might still be at risk. Always upgrade to a modern wallet that uses deterministic signatures.
Signature Malleability and How Both Networks Fixed It
ECDSA has a weird quirk: the same transaction can have multiple valid signatures. This is called signature malleability. It doesn’t let someone steal your coins, but it can break things like payment channels and smart contracts.
Bitcoin solved this with SegWit in 2017. SegWit moved the signature data out of the transaction input, making it impossible to alter without invalidating the whole transaction.
Ethereum fixed it earlier - in 2016, with EIP-155. This added a chain ID to the transaction hash, so signatures are tied to a specific network. A signature made on Ethereum Mainnet won’t work on Goerli or any other chain. This also prevented replay attacks between networks.
Both fixes were necessary. Without them, smart contracts on Ethereum and Lightning Network on Bitcoin would have been far more fragile.
Performance and Real-World Usage Numbers
Bitcoin processes around 300,000 ECDSA signature verifications per day. Ethereum? Over 1.2 million. That’s because Ethereum transactions are more complex - many involve smart contracts, token swaps, or NFT minting, each requiring its own signature.
On average, Bitcoin transactions have 0.67 signatures per transaction. Ethereum has 0.8. Why? Because Ethereum users often send multiple actions in one transaction, like approving a token and then swapping it - each needing its own signature.
Speed-wise, Ethereum’s Keccak-256 is faster than Bitcoin’s double SHA-256. But in practice, the difference is barely noticeable. Most of the delay in Ethereum comes from gas calculation and smart contract execution, not signature verification.
Hardware wallets like Ledger Nano S handle ECDSA signing in a secure chip, making them nearly immune to software attacks. User reviews on Amazon show a 4.7/5 rating for signature reliability - even during high congestion.

What’s Next? Schnorr, BLS, and Quantum Threats
ECDSA isn’t perfect. That’s why Bitcoin introduced Schnorr signatures with Taproot in 2021. Schnorr allows multiple signatures to be combined into one, making multi-signature wallets cheaper and more private. It’s better - but it didn’t replace ECDSA. It just added a new option.
Ethereum uses BLS signatures for consensus - that’s how validators prove they’ve voted in proof-of-stake. But for regular transactions? Still ECDSA. Why? Because changing the signature scheme across millions of wallets and contracts is a massive undertaking.
The real long-term threat? Quantum computers.
Shor’s algorithm can break ECDSA in hours if you have a powerful enough quantum machine. NIST estimates it’ll take 10,000 logical qubits to break a 256-bit ECDSA key. We’re not there yet. Experts say it could be 15-20 years away.
But both networks are preparing. NIST selected CRYSTALS-Dilithium as the new post-quantum standard in 2023. Ethereum Foundation researchers are already exploring how to integrate it. Bitcoin’s developers are watching closely.
Don’t panic. The transition won’t be sudden. It’ll be slow, coordinated, and backward-compatible - just like SegWit and Taproot.
Common Problems Developers Face
If you’re building on Ethereum or Bitcoin, here’s what trips people up:
- Using the wrong hash function. Don’t use SHA-256 on Ethereum - use Keccak-256.
- Forgetting chain ID in Ethereum signatures. Without EIP-155, your signature could be replayed on another network.
- Not handling signature malleability. Always use standardized libraries like ethers.js or web3.py - don’t roll your own.
- Assuming all wallets format signatures the same way. Some older clients add a recovery ID, others don’t. Always check the format.
There are over 140 questions on Bitcoin Stack Exchange about ECDSA verification failures. The top causes? Wrong hashing, wrong encoding, or mismatched public keys.
Stick to well-maintained libraries. Don’t try to implement ECDSA from scratch unless you’re a cryptographer with years of experience.
Final Thoughts: Is ECDSA Still Safe?
Yes - if you’re using modern tools.
ECDSA has been the backbone of Bitcoin and Ethereum for over a decade. It’s stood up to massive scrutiny, billions of transactions, and countless attempts to break it. The math hasn’t failed. The failures came from bad randomness, bad implementations, and outdated software.
Today, with deterministic signatures, hardware wallets, and standardized libraries, ECDSA is as secure as it’s ever been. It’s not the future - but it’s still the present. And it will be for years to come.
The next big shift will come when quantum computers arrive. But until then, ECDSA is doing exactly what it was designed to do: letting you own your money - without needing to trust anyone else.
Is ECDSA used in both Bitcoin and Ethereum?
Yes. Both Bitcoin and Ethereum use ECDSA to sign transactions. They share the same elliptic curve (secp256k1), but differ in the hash function: Bitcoin uses SHA-256, while Ethereum uses Keccak-256.
Can ECDSA be broken by quantum computers?
Yes, in theory. Shor’s algorithm on a sufficiently powerful quantum computer could break ECDSA by deriving private keys from public keys. But practical quantum computers capable of this don’t exist yet. Experts estimate it could take 15-20 years. Both networks are already researching post-quantum alternatives like CRYSTALS-Dilithium.
Why did Ethereum choose Keccak-256 instead of SHA-256?
Ethereum chose Keccak-256 because it’s faster on standard CPUs - about 15% faster than SHA-256 in benchmarks. It also has a different internal structure (sponge construction) that makes it more resistant to certain types of attacks, like length extension attacks, which SHA-256 is vulnerable to.
What happened in the 2011 Bitcoin ECDSA thefts?
Early Bitcoin wallets used poor random number generators, causing the same random value (k) to be reused across multiple signatures. This allowed attackers to calculate private keys and steal over 2,000 BTC. The issue was fixed with deterministic signature generation (RFC 6979), now standard in all modern wallets.
Are ECDSA signatures the same across all wallets?
No. While the core math is the same, different wallets and libraries format signatures differently. Some include a recovery ID, others don’t. Ethereum signatures vary by EIP (like EIP-155). Always use trusted libraries like ethers.js or bitcoinjs-lib instead of building your own signature logic.
What’s the difference between ECDSA and Schnorr signatures?
ECDSA signatures are separate and cannot be combined. Schnorr allows multiple signatures to be merged into one, making multi-signature transactions smaller and cheaper. Bitcoin added Schnorr via Taproot in 2021, but ECDSA is still used for single-signature transactions. Schnorr is more efficient, but ECDSA remains widely supported.

