Crypto Transaction Traceability Calculator
How Traceable Is Your Transaction?
Enter transaction details to estimate traceability based on the article's techniques.
Your transaction has a {score}% traceability score based on these factors:
Chain Hops: Each hop increases obfuscation. 5 hops reduce traceability by 60%.
Privacy Tools: Mixers or privacy coins can decrease traceability by 30%.
Transaction Complexity: Complex patterns like peel chains reduce visibility by 40%.
Exchange Links: KYC-linked exchanges increase traceability by 15%.
When you send Bitcoin or Ethereum, it doesn’t vanish into thin air. Every transaction leaves a permanent, public record on the blockchain. That’s not a bug-it’s the design. And that transparency is exactly what makes on-chain crypto transaction tracing possible. You don’t need to break into a vault. You just need to follow the trail.
How On-Chain Tracing Actually Works
Crypto transactions aren’t anonymous. They’re pseudonymous. That means your wallet address isn’t tied to your name, but every time you send or receive funds, that address shows up on the blockchain. And once an address is linked to a real identity-like through a KYC-verified exchange-that entire trail becomes traceable. Imagine you’re tracking a money order. You see who sent it, who received it, and where it went next. That’s what blockchain analysts do, except they’re following digital coins across thousands of interconnected transactions. Tools like Etherscan or Blockchair let anyone view these trails. But professionals use deeper tools-Nansen, Chainalysis, TRM Labs-that stitch together thousands of addresses into clusters. These clusters represent real entities: exchanges, wallets, hackers, or even individuals. The key insight? Most criminals don’t use privacy coins. They use Bitcoin and Ethereum. And those chains are wide open.The Three Main Tracing Methods
There are three ways analysts follow crypto money. Each has strengths and limits.Heuristic-Based Tracing
This is the simplest method. It uses rules of thumb based on how people actually use crypto. For example:- If a wallet receives funds from multiple small addresses and sends them all to one big exchange, it’s likely a mixer or laundering hub.
- If a wallet sends out the exact same amount to 10 different addresses right after receiving a large deposit, it’s probably a peel chain-splitting funds to hide the source.
- Most exchanges use hot wallets with predictable transaction patterns. Once you identify one, you can track where funds move next.
Rule-Based Tracing
This method builds custom detection rules from past criminal behavior. Analysts look at known ransomware wallets, darknet market addresses, or scam contracts. They then write rules to flag similar patterns. For example:- Any transaction that sends unsupported tokens to a wallet? Flag it. Scammers often do this to test if a wallet is active.
- Any address that receives funds from a known mixer and sends them to a centralized exchange within 15 minutes? High risk.
Graph Learning-Based Tracing
This is the cutting edge. Instead of rules, it uses machine learning to find hidden patterns in transaction networks. Think of it like this: you have a map of 10,000 addresses and 500,000 transactions. A human can’t see the structure. But a neural network can. It learns which addresses behave like exchanges, which act like mixers, which are likely controlled by the same person-even if they never send directly to each other. Merkle Science’s 2024 whitepaper showed this method hits 85% accuracy tracing funds across 2-3 blockchains. It’s powerful. But it needs massive data and computing power. You can’t run it on a laptop. It’s only available through enterprise platforms costing $15,000 to $50,000 per year.Where Tracing Breaks Down
On-chain tracing isn’t magic. It has hard limits.Cross-Chain Obfuscation
The biggest challenge today? Moving funds across chains. A hacker might send Bitcoin to an exchange, swap it for USDT on BSC, bridge it to Tron, then convert it to Monero. Each step requires a new tool, a new explorer, a new set of rules. Cryptoisac.org’s 2024 report says: “If at any point the trail becomes too convoluted, consider seeking expert assistance.” That’s not an exaggeration. Each bridge hop adds complexity. A single transaction might involve five different networks. Without automated cross-chain tools, tracing can take days-or become impossible.Privacy Coins and Mixers
Monero, Zcash, and privacy-focused DeFi protocols are designed to hide transaction details. In 2024, they accounted for 7.2% of all illicit crypto flows, according to CipherTrace. But even here, there’s a gap: most criminals still use Bitcoin or Ethereum for the bulk of their activity. Privacy coins are used for the final step-cleaning the last bit of tainted funds. Decentralized mixers like Tornado Cash are another hurdle. They pool funds from hundreds of users and redistribute them randomly. Chainalysis says mixers were used in 18.3% of illicit transactions in 2024. But even mixers leave traces. The same address might deposit and withdraw multiple times. Analysts can spot these patterns-even if they can’t link the input to the output.The Attribution Problem
Here’s the truth no one wants to admit: you can’t prove who owns a wallet just from on-chain data. You can cluster addresses. You can say “this group of 200 wallets acts like one entity.” You can even say “this entity sent funds to a known ransomware operator.” But unless you tie it to KYC data, IP logs, or a seized device, you can’t say “John Doe owns wallet 0x789…” Dr. Sarah Meiklejohn from UCL put it bluntly: “The attribution problem remains fundamentally unsolved.” Tracing gives you the path. But you need outside evidence to name the person walking it.
Who Uses These Techniques?
It’s not just law enforcement.- Exchanges: 87% of crypto exchanges now use blockchain analytics to flag risky deposits. If your wallet has ever sent money to a mixer, you might get frozen.
- Banks: 63 of the top 100 global banks monitor crypto transactions. They need to comply with FATF’s Travel Rule, which requires them to track transfers over $1,000.
- Insurance companies: If a company gets hacked, they hire forensic analysts to trace stolen funds and recover assets.
- Traders: Some use tracing to avoid wallets linked to scams or insider dumps.
Tools of the Trade
You don’t need a government budget to start tracing. But you need the right tools.- Free explorers: Etherscan, Solana Explorer, Blockchair. Good for basic lookups.
- Professional platforms: Nansen, Elliptic, TRM Labs. These show wallet clusters, risk scores, and cross-chain flows.
- Open-source tools: BlockSci, Chainalysis Reactor. Used by researchers and forensic teams.
The Future: AI and the Arms Race
The next big leap? Generative AI. Gartner predicts that by 2027, 70% of blockchain analytics tools will use AI to detect anomalies automatically. Instead of waiting for a rule to be written, the system will learn what “normal” looks like-and flag anything unusual. But criminals aren’t standing still. They’re using AI too-generating fake transaction patterns, creating synthetic wallets, and automating fund movement across dozens of chains. David Jevans of CipherTrace says: “The tracing arms race will continue indefinitely.” Every improvement in detection leads to a new obfuscation technique. And vice versa.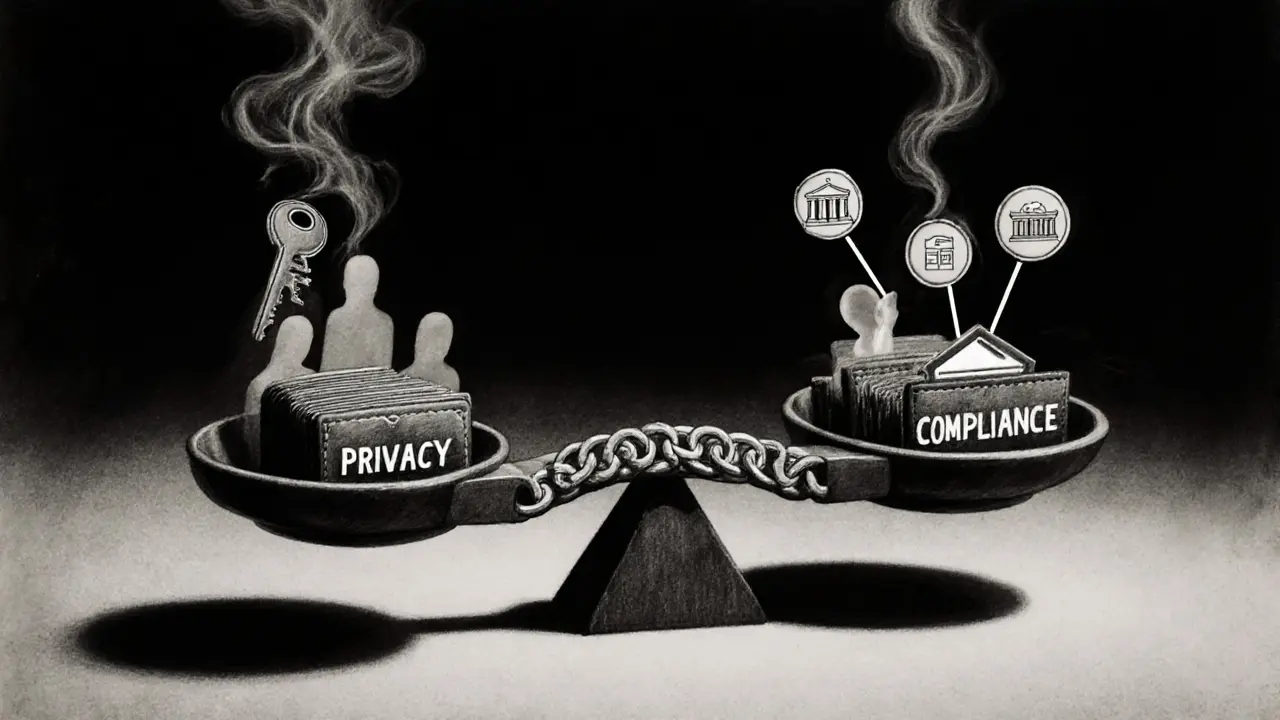
Privacy vs. Compliance
There’s a tension here. On one side, regulators want to stop crime. On the other, privacy advocates warn that mass tracing could turn crypto into a surveillance tool. The Electronic Frontier Foundation argues that “these tools shouldn’t be used to surveil legitimate financial activity.” That’s a fair point. If you’re just buying coffee with Bitcoin, your transaction shouldn’t be flagged just because someone else used the same exchange. The challenge is building systems that target bad actors-not ordinary users. Right now, most tools rely on risk scores. A wallet linked to a mixer gets a “high risk” label. But that doesn’t mean it’s criminal. It just means it’s suspicious.What You Can Do
If you’re a trader or holder:- Avoid wallets with known links to mixers or scams.
- Don’t reuse addresses. Each new transaction should use a fresh one.
- If you’re using a centralized exchange, your activity is already traceable. Don’t assume you’re anonymous.
- Use privacy tools like CoinJoin or privacy-focused wallets only if you understand the trade-offs.
- Start with free explorers. Learn how transactions are structured.
- Study past cases. The Bitcoin Pizza transaction? The Mt. Gox hack? The Lazarus Group? These are textbook examples.
- Don’t rely on one tool. Use multiple platforms to cross-check.
- Remember: tracing gives you the path. You need external evidence to name the person.
Final Thought
On-chain tracing works because crypto is transparent. That’s its strength-and its weakness. You can’t hide what you broadcast to the world. But you also can’t prove identity without stepping outside the chain. The future won’t be about perfect tracing. It’ll be about smarter detection. Better tools. Stronger collaboration between exchanges, regulators, and analysts. And a constant push-and-pull between those trying to follow the money-and those trying to erase the trail.For now, the ledger never forgets. And someone is always watching.


This is why crypto is a joke. You think you're anonymous but you're just dancing on a live camera feed. Everyone's watching. Everyone. And they're not even trying to hide it.
I just wish people understood that tracing isn't about control. It's about accountability. If you're not doing anything shady, why be scared of a public ledger?
The ontological framework of blockchain transparency fundamentally reconfigures the epistemology of financial anonymity. Pseudonymity is not anonymity-it's a hermeneutic veil, a semiotic mask that collapses under ontological scrutiny when cross-referenced with KYC metadata matrices. The blockchain doesn't lie. It merely refracts identity through distributed consensus.
Okay so like, I get that tracing works but also... who even cares? I mean, if I buy coffee with BTC, does it really matter if some algorithm tags my wallet as 'suspicious' because I used the same exchange as a hacker? Like, what's next? My toaster gets flagged for buying crypto last Tuesday?
Tracing is inevitable. Better to learn it than fight it. Start with Etherscan. Watch how coins move. It's like learning chess.
I read this whole thing and honestly? I’m not sure I got anything out of it. It’s like someone wrote a textbook chapter and then said ‘just post it’. No flow, no personality, just walls of jargon. I think I need a nap now.
lol i just tried using etherscan and i think i clicked the wrong button and now my screen is full of hex code. help? i just wanted to see where my eth went. also i think i spelled 'transaction' wrong in the title lol
In India, we see this every day. People think crypto is magic money. But the truth? It’s just money with more steps. And the steps leave footprints. No magic here, just math.
One thing people forget: tracing tools are only as good as the data they're fed. If you're using a mixer, you're not invisible-you're just making the detective's job harder. And they're getting better. Fast.
Look I’m not here to judge anyone’s crypto habits but I’ve seen wallets get flagged for no reason and people lose access to their funds for months. It’s not about crime anymore. It’s about overreach. The system doesn’t distinguish between ‘suspicious’ and ‘innocent’-it just labels. And once you’re labeled, you’re guilty until proven innocent. And good luck proving innocence to a machine.
I just want to say... I really appreciate how thorough this breakdown is. It's so easy to get lost in the hype, but this reminds me that transparency isn't inherently bad-it's just powerful. And power needs responsibility. I hope regulators and developers remember that as these tools grow. We don't want to build a world where every transaction is monitored... but we also can't ignore the real harm that untraceable funds enable. There's a middle ground. I believe in it.
AI tracing is coming and honestly? I'm not scared. I'm curious. Like... if a bot can track my wallet better than my ex tracked my location... maybe that's just progress? Or maybe we're all just ants in a digital ant farm. Either way... I'll keep using BTC. But I'll stop reusing addresses. Just in case.
Let’s be real-this whole tracing thing is just corporate surveillance dressed up as law enforcement. Chainalysis? Nansen? They’re private companies with zero accountability. They’re not cops. They’re data brokers selling risk scores to banks and exchanges. And guess who pays the price? Regular users. You think your wallet is safe because you didn’t use Tornado Cash? Wrong. Your exchange already flagged you the second you bought ETH. They don’t need to trace you. They already know.
And don’t even get me started on the ‘criminals use Bitcoin’ narrative. That’s the whole point. Bitcoin is public. Monero is private. So why are the bad guys still using Bitcoin? Because it’s easier. Because the system is designed to be open. And now the system is weaponizing that openness to punish everyone who touches it. This isn’t justice. It’s control. And it’s being sold to us as safety.
They say ‘if you have nothing to hide, you have nothing to fear.’ But what if you just want to be left alone? What if you’re not a criminal-you’re just a person who wants to own their own money? That’s not a crime. But according to these tools? It’s a risk score.
And the worst part? No one’s asking us. No public vote. No debate. Just a bunch of tech bros in San Francisco deciding what ‘suspicious’ means. And then banks freeze accounts. And then people lose their life savings. All because a machine saw a pattern it didn’t like.
So yeah. Trace all you want. But don’t pretend you’re protecting society. You’re just building a financial police state. And we’re all the suspects.
EVERYTHING is tracked. Even your phone. Even your fridge. Crypto is the only thing left that isn’t fully owned by the government. And now they’re coming for it. They don’t want you to have privacy. They want you to be a transparent slave. This isn’t about crime. It’s about control. The blockchain is the last free space. And they’re trying to turn it into a Walmart receipt.